March 2, 2026
Tracking CyberStrikeAI Usage
Team Cymru is continuously monitoring our global netflow visibility to uncover patterns of adversary activity, identify malicious operations, and gain actionable intelligence. In this post, we are diving into CyberStrikeAI, an open-source artificial intelligence (AI) offensive security tool (OST) developed by a China-based developer who we assess has some ties to the Chinese government.
What is CyberStrikeAI?
In its own words from the GitHub repository (see here), “CyberStrikeAI is an AI-native security testing platform built in Go. It integrates 100+ security tools, an intelligent orchestration engine, role-based testing with predefined security roles, a skills system with specialized testing skills, and comprehensive lifecycle management capabilities.”
CyberStrikeAI comes with its own dashboard that helps users quickly understand the platform's core features and current state, as shown in Figure 1 below.

CyberStrikeAI was first brought to our attention following the Amazon CTI team’s blog about AI-augmented threat actor infrastructure they had discovered. Amazon shared this related IP 212.11.64[.]250.
Analysis of that IP address in Team Cymru Scout’s open port scan data revealed that it had this “CyberStrikeAI” banner running on this service, as shown in Figure 2 below.

Identifying Targeting with NetFlow
Using Team Cymru Scout, we can find NetFlow communications between the IP shared by Amazon and its targets, such as the Fortinet FortiGate devices it was observed targeting, as shown in Figure 3 below.

Researching Ed1s0nZ
While researching the GitHub profile (see here) of CyberStrikeAI’s developer, “Ed1s0nZ”, several attributes about the individual caught our attention.
Firstly, Ed1s0nZ’s other GitHub repositories suggest interest in exploitation activity:
- watermark-tool: A secure and efficient invisible document watermarking solution that can add completely invisible digital watermarks to various documents, while supporting watermark extraction and verification. Developed in Go, it supports both web and CLI usage. The watermark uses steganography technology to ensure that the watermark is completely invisible and does not affect the reading experience and visual effects of the original document.
- PrivHunterAI: This tool uses a passive proxy approach and mainstream AI (such as Kimi, DeepSeek, GPT, etc.) to detect privilege escalation vulnerabilities. Its core detection function is built on the open APIs of the relevant AI engines and supports data transmission and interaction via HTTPS protocol.
- InfiltrateX: A useful privilege escalation scanning tool. While automated detection of privilege escalation vulnerabilities is difficult, prone to occur, and poses serious risks, it can still strive to automate the detection of some such vulnerabilities.
Further, Ed1s0nZ’s GitHub activities indicate they interact with organisations that support potentially Chinese government state-sponsored cyber operations. This includes Chinese private sector firms that have known ties to the Chinese Ministry of State Security (MSS).
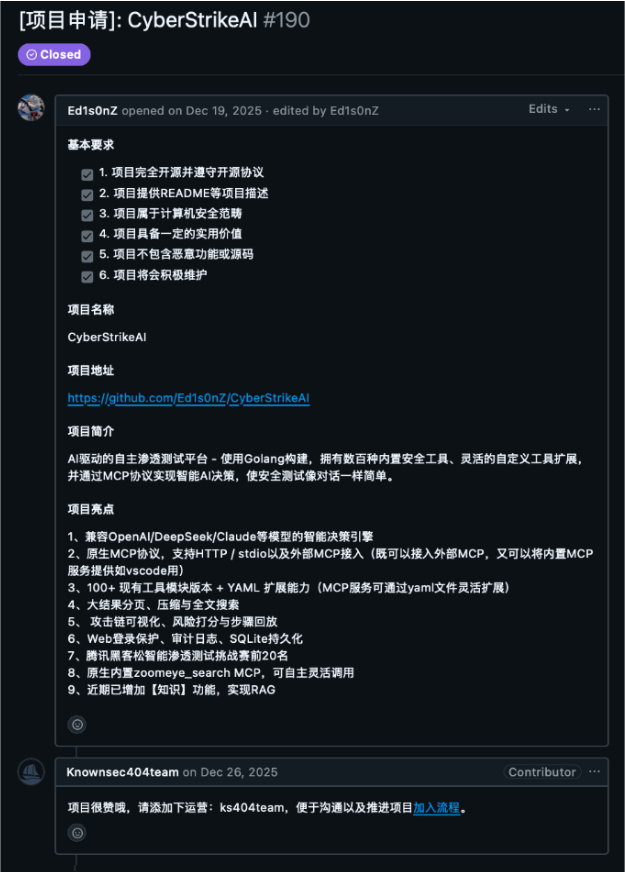
A number of GitHub activities potentially link Ed1s0nZ to the Chinese state-sponsored cyber operations. On 19 December 2025, Ed1s0nZ posted CyberStrikeAI to Knownsec 404’s Starlink Project, as shown in Figure 4 below. Based on published reporting by DomainTools and others, Knownsec does work for the MSS and the Chinese People’s Liberation Army (PLA).
Further, on 5 January 2026, Ed1s0nZ added to their GitHub profile “CNNVD(国家信息安全漏洞) 2024 年度漏洞奖励计划 · 二级贡献奖(个人). Translation: CNNVD (Chinese National Vulnerability Database) 2024 Vulnerability Reward Program - Level 2 Contribution Award (Individual).” The CNNVD is run by CNITSEC and is also overseen by the MSS. Arguably, this program exists as a vehicle for the CCP to collect zero days before they are publicly disclosed, as detailed by researchers at BitSight.
Interestingly, we noticed Ed1s0nZ removed the reference to the CNNVD from their GitHub profile, potentially in effort to cover up these ties to one of these MSS-affiliated organisations.
Number of IPs Over Time
While researching CyberStrikeAI, we noticed that the repository was first added on 8 November 2025, as shown in Figure 5 below.. We did not observe a lot of IPs running the platform around this date though.

However, from 20 January 2026 to the conclusion of this assessment on 26 February 2026, we observed 21 unique IP addresses running CyberStrikeAI, over differing periods of time, as shown in Figure 6 below.

Where users hosted CyberStrikeAI
Many of the CyberStrikeAI servers were hosted in Chinese-speaking locals, namely China, Singapore, and Hong Kong. Which is to be expected for a tool developed by a Chinese-speaking coder.

Outlook
Based on our analysis, the adoption of CyberStrikeAI is poised to accelerate, representing a concerning evolution in the proliferation of AI-augmented offensive security tools. While the GitHub repository was initially created in November 2025 with minimal active deployments, the rapid emergence of 21 unique IP addresses running the platform between January 20 and February 26 indicates a sharp increase in operational usage. Because the platform is heavily hosted in regions like China, Singapore, and Hong Kong, we anticipate that CyberStrikeAI will continue to see strong adoption among Chinese-speaking threat actors.
Furthermore, the developer’s (Ed1s0nZ) documented interactions with organizations affiliated with the MSS, specifically Knownsec and the CNNVD, suggest a high likelihood that this tool may be leveraged by Chinese state-sponsored advanced persistent threats (APTs). The developer's recent attempt to scrub references to the CNNVD from their GitHub profile points to an active effort to obscure these state ties, likely to protect the tool's operational viability as its popularity grows.
As adversaries increasingly embrace AI-native orchestration engines, we expect to see a rise in automated, AI-driven targeting of vulnerable edge devices, similar to the observed reconnaissance and targeting of Fortinet FortiGate appliances. In the near future, defenders must be prepared for an environment where tools like CyberStrikeAI, alongside the developer's other AI-assisted privilege escalation projects like PrivHunterAI and InfiltrateX, significantly lower the barrier to entry for complex network exploitation. Security teams should proactively monitor their environments using the provided IP indicators and prepare for the continued weaponization of AI in offensive cyber operations.

.png)
.png)
.png)