April 2, 2026
Cyber Security Intelligence: Analysis of Edge Devices Amid Growing Vulnerabilities
Recently, AWS published a report on a newly disclosed vulnerability affecting Cisco Firewall Management Center (CVE-2026-20131), with exploitation of its MadPot honeypot system detected in the wild. According to the AWS CTI team, exploitation activity dates back to at least January 26, even though Cisco did not release a patch until March 4.
This is the latest in a growing series of critical vulnerabilities affecting major security vendors and edge devices in 2026, including:
- CVE-2026-1281 — Ivanti Endpoint Manager Mobile (EPMM) — Published January 29, 2026: Critical unauthenticated remote code execution/code injection vulnerability. Ivanti stated that a limited number of customers had already been exploited, and CISA added it to the KEV catalog the same day.
- CVE-2026-1340 — Ivanti Endpoint Manager Mobile (EPMM) — Published January 29, 2026: Critical unauthenticated remote code execution/code injection vulnerability disclosed alongside CVE-2026-1281. Vendor and public analysis later described both flaws as actively exploited.
- CVE-2026-24858 — FortiOS / FortiGate— Published Januaruy 27, 2026 (also affecting FortiManager, FortiAnalyzer, FortiProxy, FortiSwitchManager, and FortiWeb when FortiCloud SSO is enabled): Critical authentication bypass/improper access control vulnerability via FortiCloud SSO. It allowed an attacker with a FortiCloud account and a registered device to access devices registered to other accounts. Fortinet stated that the issue had been exploited in the wild prior to disclosure.
And we are still not even out of Q1.
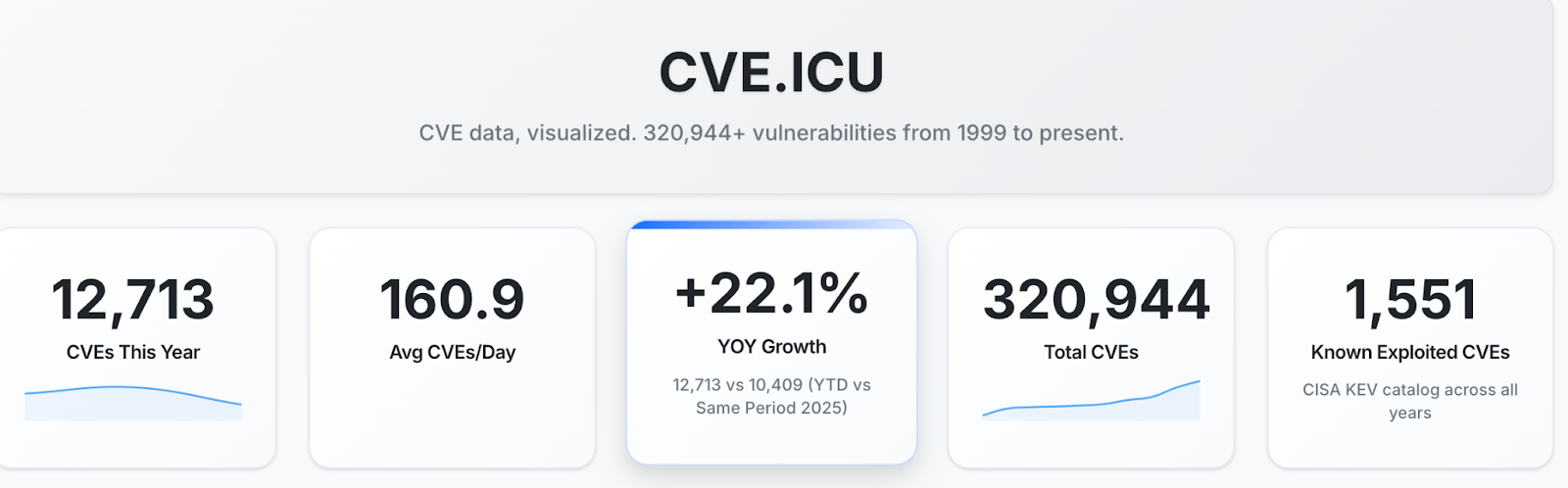
According to cve.icu, an excellent resource maintained by Jerry Gamblin, as of this writing 2026 has already seen 22% more published vulnerabilities than the same period in 2025.
That raises an obvious question: what has Team Cymru observed in the last 30 days?
A Quick Note on Tagging
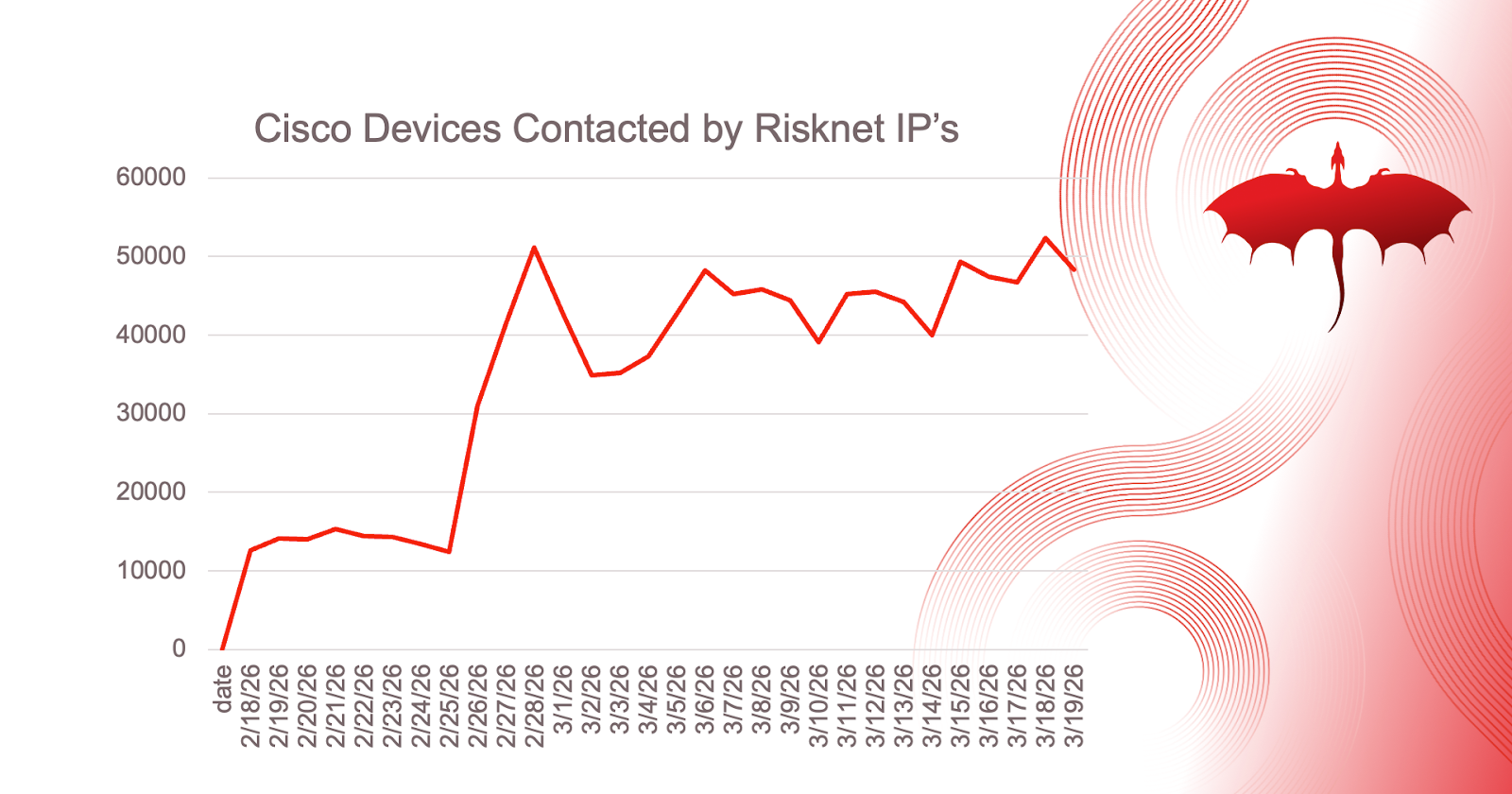
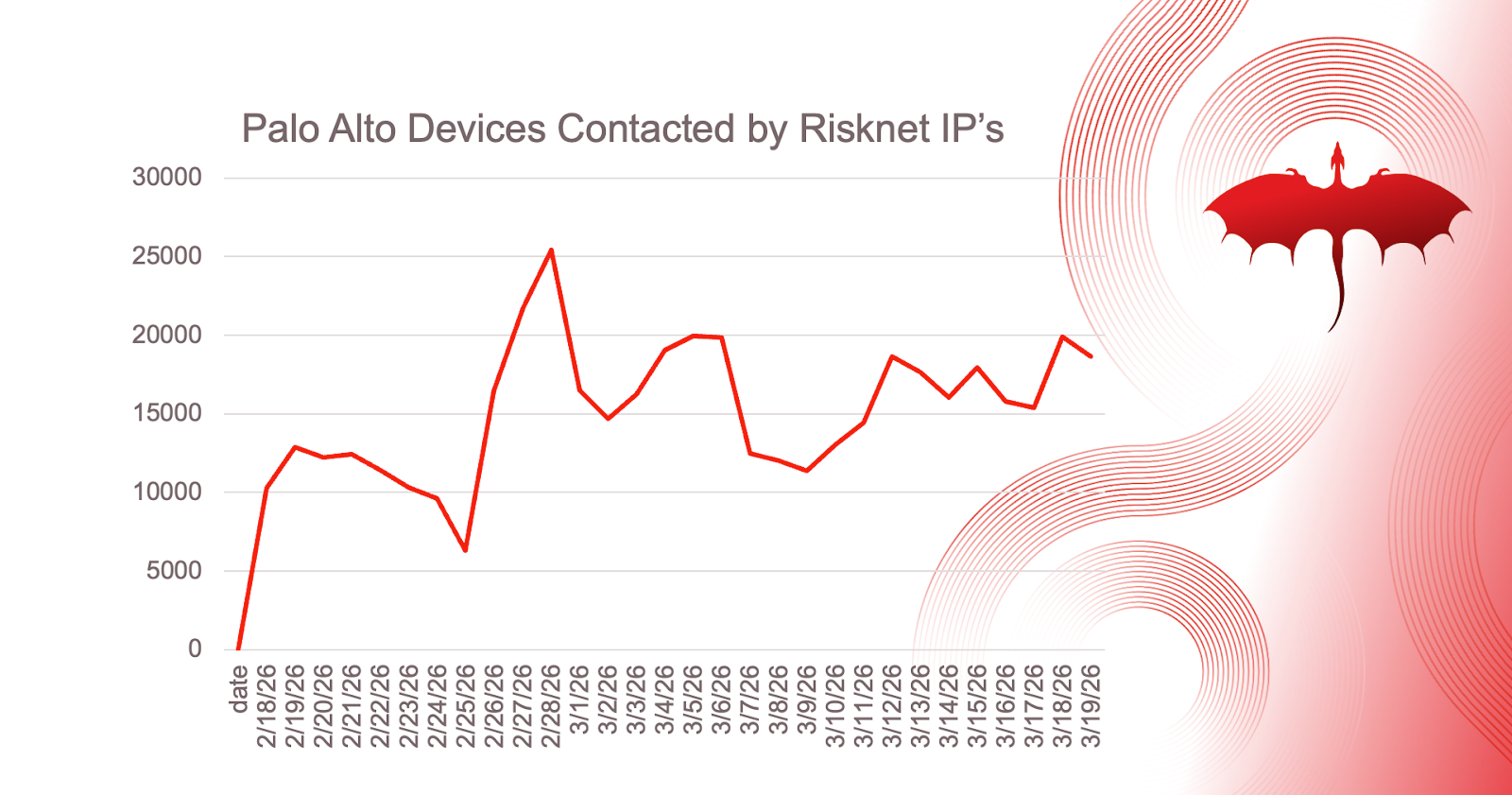
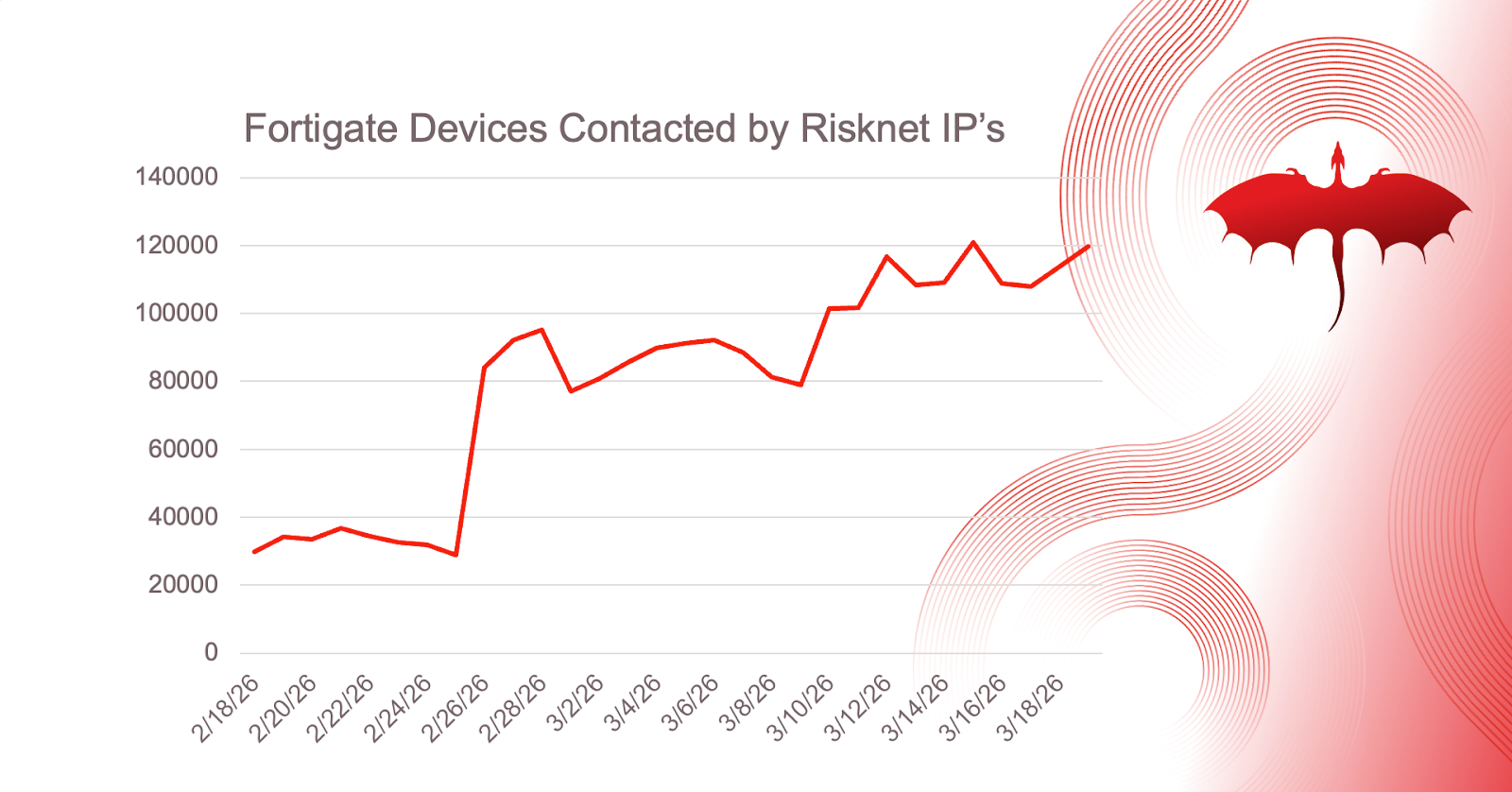
Team Cymru maintains extensive visibility into tagged infrastructure across a wide range of categories, including networking devices, VPNs, malware, and offensive security tooling. As part of that work, we assign a Risknet tag to IPs within subnets that exhibit a sufficient level of concerning or malicious activity.
When that tagging is combined with our unique NetFlow visibility, it becomes possible to identify meaningful traffic patterns at scale. For this analysis, we examined several high-profile VPN and edge device technologies to determine how frequently they were being contacted by IPs tagged as Risknet. Historically, Risknet traffic has often preceded exploitation, compromise, and follow-on activity such as ransomware or extortion.
What Devices are Risky IPs Contacting?
Overall, we observed a notable increase in flows from Risknet-tagged IPs beginning in late February 2026. That pattern was visible across four of the device types we reviewed.
Ivanti and Citrix, however, stood out.
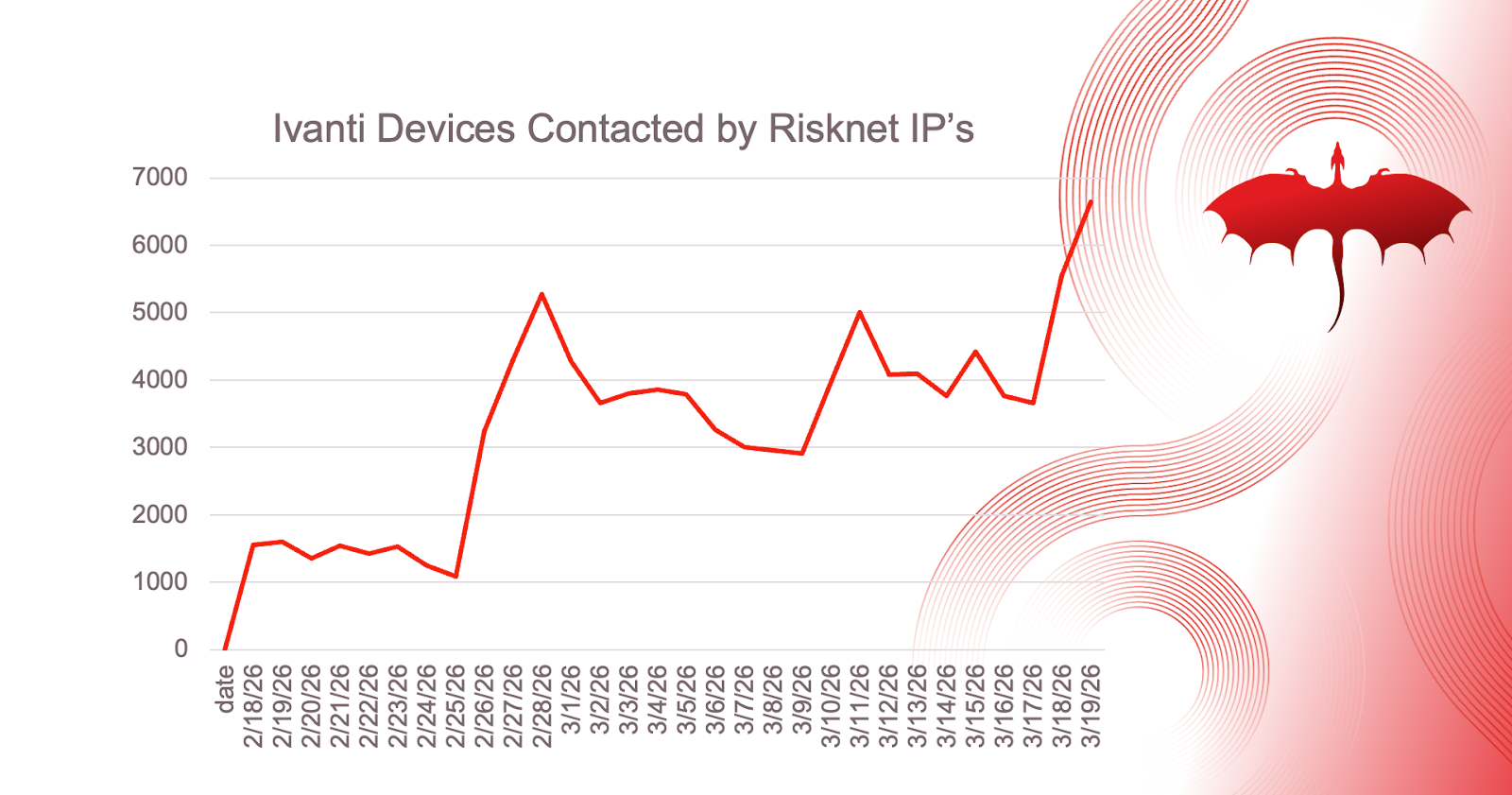
In the closing days of March 2026, Ivanti devices showed a significantly sharper rise in connection attempts from Risknet infrastructure than the other VPN platforms included in this review. That does not, on its own, confirm a new exploitation campaign, but it does point to elevated risk and a need for heightened attention from operators of Ivanti Connect Secure and other internet-facing VPN appliances.
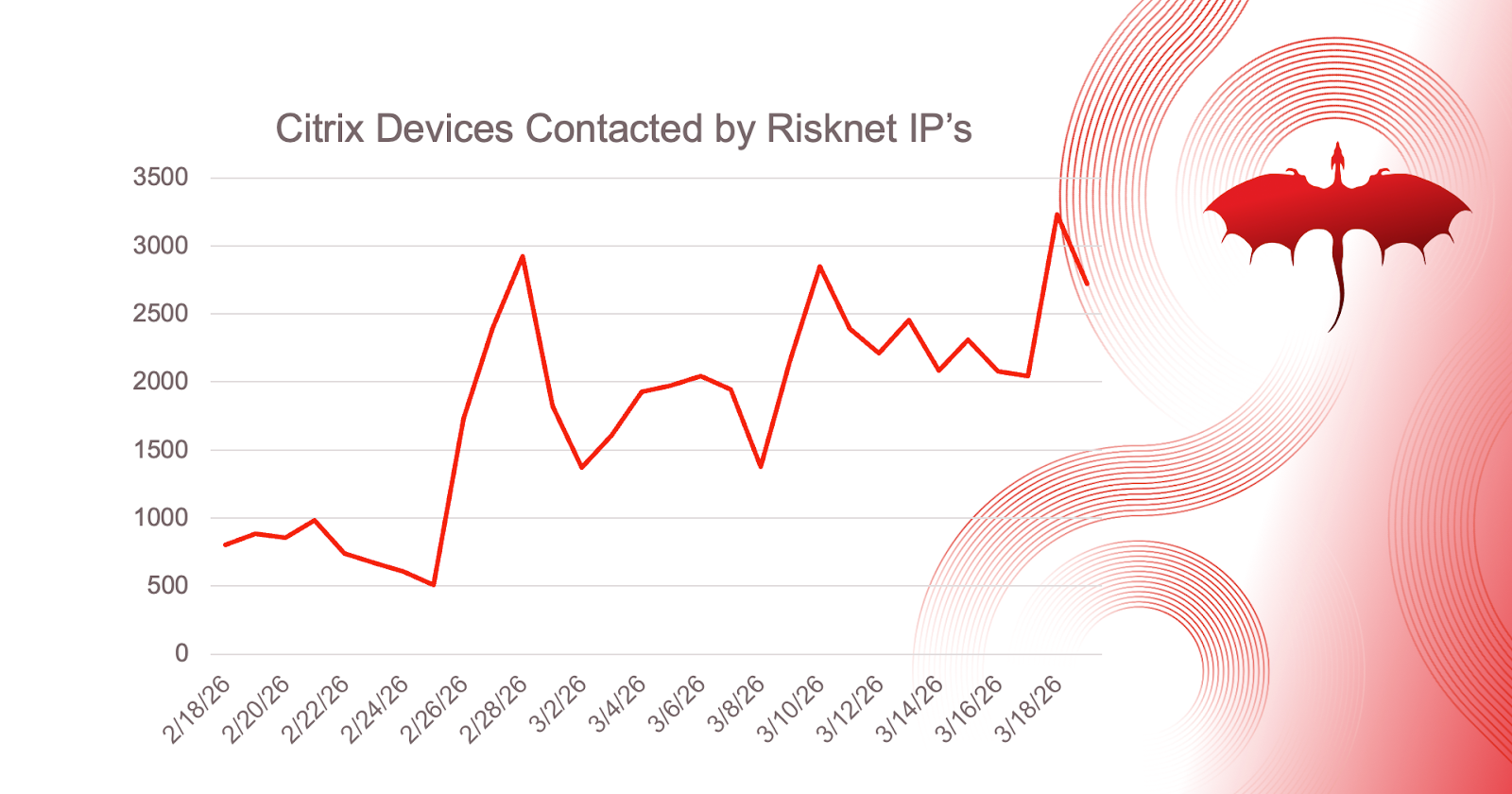
Citrix devices also showed a significant spike during this research period. Shortly after concluding the data collection, Citrix reported a new critical vulnerability, CVE-2026-3055. This vulnerability allows unauthenticated attackers the ability to potentially leak memory, similar to previously disclosed “Citrix Bleed” vulnerabilities.
How Should Organizations Harden Edge Appliances
For defenders, the takeaway is straightforward: Ivanti devices are currently attracting materially more attention from potentially malicious infrastructure than comparable VPN platforms. At a minimum, operators should treat this as a signal to review exposure and harden their environment.
Additionally, we observed Citrix devices also getting an inordinate amount of attention from Risknet IP’s leading up to the reports of a new critical vulnerability.
Organizations running VPN and edge appliances should ensure systems are fully patched, verify that management interfaces are not exposed to the internet, and review logs and telemetry for signs of suspicious activity. Exposed management access has repeatedly been a common entry point in attacks against VPN infrastructure.
The bottom line: monitor these devices closely, reduce exposure wherever possible, and patch now before elevated scanning turns into confirmed compromise.


.png)
.png)