April 22, 2026
Unmasking DPRK Cyber Threat Actors: Fake IT Worker Infrastructure & Post-Exposure Analysis
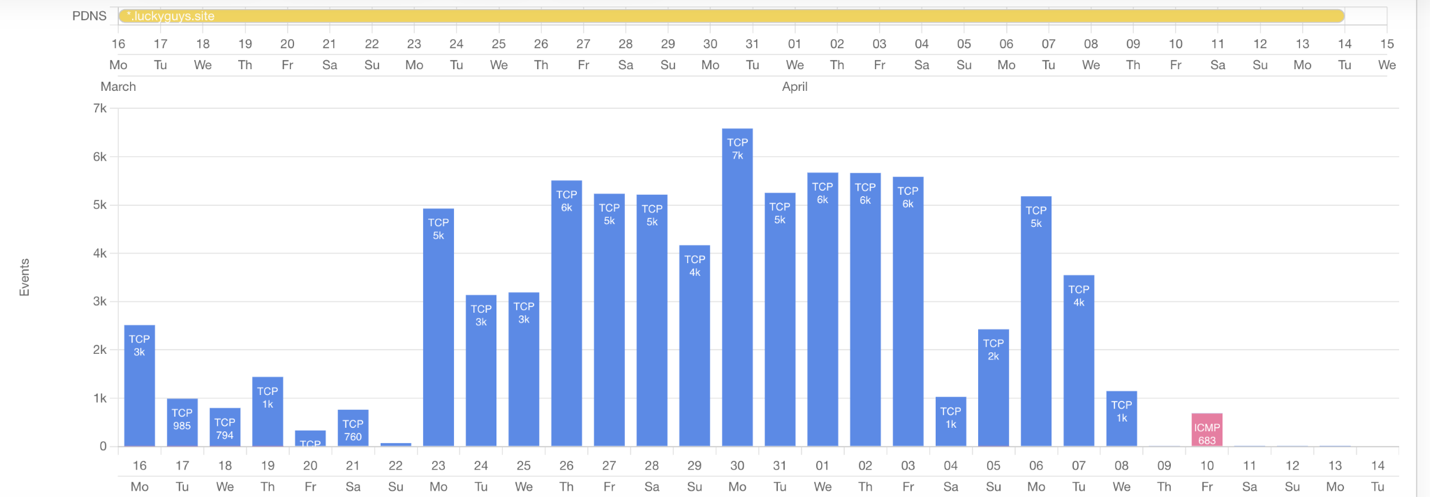
This investigation was initiated after reporting by cryptocurrency security researcher ZachXBT, who identified the domain luckyguys[.]site as being linked to payments associated with DPRK-linked fake IT workers. At the time of analysis, the domain resolved to 163.245.219[.]19, and this report examines 30 days of network activity associated with that infrastructure.
ZachXBT has an established track record of uncovering illicit financial activity within the cryptocurrency ecosystem, with prior disclosures frequently correlating with subsequent law enforcement action. As such, infrastructure identified in his reporting warrants heightened scrutiny.
VPN Usage Patterns
Analysis of VPN-related connections to the identified IP revealed a highly concentrated usage pattern:
- Astrill VPN: 37.5%
- Mullvad: 32.25%
- Proton VPN: 6.25%
The prominence of Astrill VPN is notable, as it has been repeatedly associated with DPRK IT worker activity in prior reporting by organizations such as GitLab and Flare.io.
Temporal analysis further showed that traffic to the IP dropped off sharply following public exposure on April 8. This pattern is consistent with known threat actor behavior, where infrastructure is rapidly abandoned once publicly attributed.
Residential IP Analysis
American and Latvian residential IP addresses were observed communicating with the infrastructure during the analysis period.
Netflow analysis of these IPs revealed:
- Frequent use of Astrill VPN
- Connectivity to cloud services associated with:
- Gmail
- ChatGPT
- Workana
The use of ChatGPT aligns with recent findings from Group-IB, which reported DPRK-linked IT workers leveraging AI tools to assist with development tasks and communication.
Freelance Platform Correlation
Workana, a freelance platform focused on remote talent, appears prominently in the observed network activity. The platform’s positioning as a hub for remote IT work makes it a viable channel for threat actors seeking to obtain employment under false identities.
This observation is further supported by prior research from Nisos, which documented DPRK-affiliated operators maintaining freelancer profiles on platforms like Workana to obtain remote employment under false identities.
Additional IP Uncovered
Analysis of other X509 certificates with the name “luckyguys[.]site” found a second IP that was not part of any previous reporting hosted on 216.158.225[.]144. This IP also demonstrated a significant drop in traffic after the publication of the report by ZachXBT and aligned with the threat actor abandoning infrastructure post-attribution.
Key Assessment
The combined network telemetry, VPN usage patterns, and residential IP distribution strongly suggest:
- A distributed network of remote IT workers or facilitators
- Likely use of home-based systems or “laptop farms”
- Active participation in sanctions evasion workflows
- Operational overlap with known DPRK fake IT worker tradecraft
The rapid cessation of activity following public exposure reinforces attribution confidence and indicates adversary sensitivity to visibility.
Implications for Organizations
Organizations should take the following into account:
- Residential IP addresses are not inherently trustworthy and may be part of proxy or laundering networks
- VPN overlap—particularly with providers previously linked to DPRK activity—should be treated as a risk signal
- Freelance hiring pipelines (especially via global platforms) represent a key infiltration vector
- Monitoring for behavioral patterns, not just indicators, is critical for detection
- Identify any network traffic connecting (including corporate machines) connecting to the IP’s 216.158.225[.]144 and 163.245.219[.]19.
Special caution should be applied to residential IPs that also exhibit proxy-hosting behavior (e.g., proxyline usage), as these may represent shared infrastructure supporting malicious operations.
References:
https://6068438.fs1.hubspotusercontent-na1.net/hubfs/6068438/dprk-it-worker-scam-mitigation.pdf
https://www.group-ib.com/blog/dprk-fake-remote-developers/
https://about.gitlab.com/blog/gitlab-threat-intelligence-reveals-north-korean-tradecraft/
https://flare.io/learn/resources/north-korean-infiltrator-threat


.png)
.png)