June 17, 2020
Network Perimeters in the Age of Social Distancing
The COVID-19 pandemic has turned our world upside down, leaving many of us to question whether we will ever see “normal” again. One concept, we’ve all become familiar with recently is “Social Distancing”. The CDC describes this as “physical distancing”, meaning to keep space between yourself and other people outside of your home.
For me, this idea of maintaining separation parallels our computer technical term for the concept of a DMZ, or De-Militarized Zone. Let me explain:
DMZ
It doesn’t matter when you have started your interest in networks, or even your formal career in information security, we all start with the concept and theory of a DMZ. My first encounter with the computerized version of the DMZ name was from the book “Computer Networks” by the brilliant authors Andrew S. Tanenbaum and David J. Wetherall. Even though the first edition of this book dates back to the early eighties, even then the authors described the security topology and the benefits of having a separation between networks and devices.
Incidentally, if you have a passion for military history and this topic of the DMZ you need to have on your to-do list a visit to the ‘other’ DMZ in South Korea – it’s totally worth it! Here is your author on a recent trip there himself:

R0
Another new term that was also new for many of us this year was the epidemiological term of R0, pronounced R nought or just R zero. We can understand this as the expected number of infections directly generated by one infected person in a population, where all people are susceptible to the spread of infection. This can be easily translated into a network security analogy, as we see this daily in our work with infected machines scanning for other vulnerable machines and spreading malicious code as infections.
If you turned to your interactive device of choice in recent months, you also may have stumbled onto the numbers of infected persons, such as the COVID-19 Dashboard by the Center for Systems Science and Engineering (CSSE) at Johns Hopkins University (JHU).
This illustrates that by the end of May 2020 we had 6,152,160 confirmed cases of COVID-19 (the name of the disease you get from the SARS-CoV-2 virus), and that includes the number of active cases as well the number of recovered cases [2].

https://gisanddata.maps.arcgis.com/apps/opsdashboard/index.html#/bda7594740fd40299423467b48e9ecf6
But what about computers?
Is there value in measuring computer infections in a similar way?
Not only do we measure this, but we also classify them according to different categories and classes of “maliciousness”, based on what they do, what type of code they use, and how they operate.
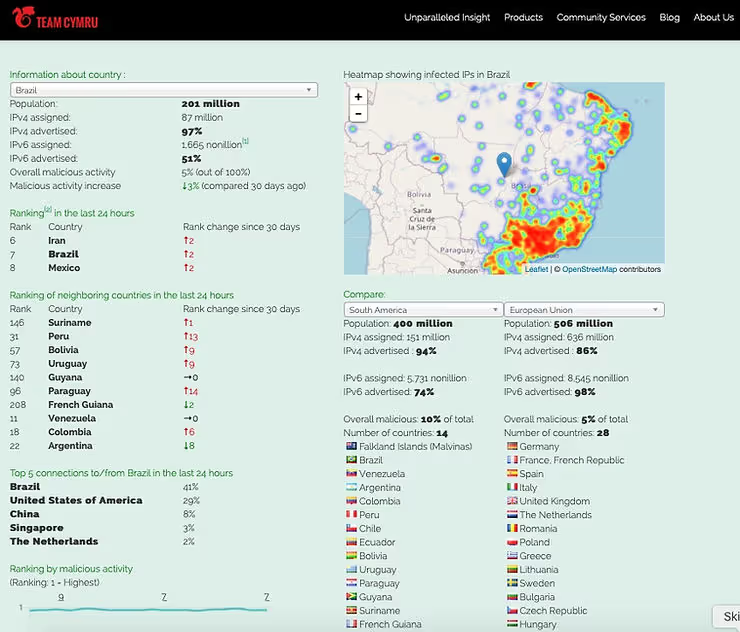
Team Cymru World Hackbook
Looking into Team Cymru data we reported during the full month of May 2020, 44,441,438 IP “occurrences”. This includes multiple reports about the same IP. We share these reports — at no cost — with National Computer Security Incident Response Teams (NCSIRTs), which are members of our CSIRT Assistance Program (CAP).
If you compare those numbers with populational numbers, just for clarity, we can consider 3.7 billion usable IPv4 IPs – 3,706,452,992 and 7.8 billion humans you can see how these numbers are numerically significant. If you are a National CSIRT and not yet a member of our CSIRT Assistance Program, please contact the Jacomo via outreach at cymru.com to join the 124 existing CAP members.
Social Distancing
When WHO.int started to advise and promote social distancing, I took a look at our data, trying to see if I could find infected IPs talking to the websites of WHO[.]int

(22-Feb-2020 to 31-May-2020 total of 4642 IPs)
From the time period 22-Feb-2020 to 31-May-2020 we saw 4,642 “infected” IPs that met this criteria. As a security practitioner I would not be comfortable with knowing an infected IP in my network is also probing who[.]int for unauthorized access.
The definitions of network perimeter, DMZ, internal network and external network, have evolved a great deal over recent years, especially with the advent of modern cloud-based solutions, and it is time for us to also consider enhancements to the traditional ‘next-hop protection’. We need to take the blinders off and take expand our visibility to include the signal on the network hops reaching out to our “new perimeters”, whereverthey are now located. In today’s world, if you only see the next-hop-network, then you are underestimating your adversaries in the complex cat and mouse game played every minute on the Internet. Incidentally, we help our partners and clients go beyond the next hop, in order to gain the visibility they need.
One old and misleading assumption that must be debunked is the notion that you will have adequate defense by simply using a deny list to prevent malicious IPs from accessing your infrastructure. I will share one example of how this is easily bypassed:

This is a cropped print-screen of a criminal hacking service that offers compromised systems and one of the many features and guarantees provided by those criminals is that the systems will not show on blacklists. From a criminal perspective, if I need a clean IP to position myself one-hop before a target infrastructure this is easily done for USD $7.50 – this will circumvent your deny lists and geographical access restrictions.
Conclusion
Paraphrasing the US Marines: “Improvise, Adapt, and Overcome”…more than ever, we need to constantly assess our connected footprint and review our network and security strategy to protect our digital assets. If you don’t already have in place today worst-case scenario detection, protection and reaction methods that include visibility beyond the next hop, you are tempting fate.


.png)
.png)